Application Realization, the Only Unified Approach to Application Management
Enable your security team to increase operational maturity
What are Applications?
Given the myriad of solutions that claim to manage, protect, or create applications, there is a surprising amount of confusion on what an application actually is. Technologies including application discovery, dependency mapping, and performance management provide distinct viewpoints of an application, as well as the basis for decisions about an application’s lifecycle. However, these differing viewpoints result in confusion, as there is no consolidated and comprehensive understanding of the application. Organizations unable to understand their applications consequently struggle to identify the impact of changes to the applications, the risk of the applications, and whether the applications even serve a business purpose. This confusion can result in the form of application outages, successfully executed attacks, and overages in cloud expenditures.
The Purpose of Applications
Applications are a grouping of complex connections that consist of the servers and components that serve them, but the most important connections are to business processes and revenue. Applications support the operation of the business, the growth of the business, the employment of the business, and success of the business — either to itself or its investors. So to understand an application, one must understand the business.
Applications are built with the guidance and efforts of stakeholders. Existing applications were built to support an important process of the business to increase efficiency or drive revenue. Applications were built with resiliency to meet their intended usage. Application infrastructure and compute resources were chosen to support the application. Application development was executed in a manner to ensure cost effective usage of resources. Each of these data points are not technical in origination – they are collaboratively constructed data points to address business-specific goals.
Application Discovery… Problem Solved?
Too often in technology, general terms are overused in an attempt to communicate technical concepts. Marketers enthusiastically assert products that “quickly identify applications!” or “automatically discover applications anywhere!”. Application discovery, mapping, and dependency tools are often at the forefront of these marketing claims. Application discovery solutions that rely on network flows, network policies, or tags may identify a profile of an application but do not understand what the application is, what the application does, and the application’s significance to the business. This context is critical, as very few individuals in an organization will recognize IP addresses, cryptic service names, or other granular information that is only valid in one domain or to a single stakeholder in the organization. The reality is that no software available today can read the minds of developers, understand decades of infrastructure changes, or determine the business rationale for the development of an application.
APPLICATION DISCOVERY IS A MYTH.
While it may be disappointing to hear that application discovery is not grounded in reality, it does not mean that the ideas of comprehensive application visibility, connection discovery, and business contextual attribution are fictional. What is required is to approach the problem from both a technical and business perspective. Application Realization is the convergence of two perspectives – the technical and the human – and it is imperative that both perspectives are equally represented in a complete profile.
Application Realization… Problem Solved.
Applications are more than merely groups of servers, as applications serve business-specific purposes tied to revenue, provide continuity in operations, and require financial and resource commitments. Application Realization enables organizations to converge the technical attributes of applications with business-specific context in order to realize the perspectives of multiple stakeholders for a complete profile of an application. Obtaining this critical application information empowers organizations to determine which applications are most critical to the business, which applications are candidates for refactoring, and which applications should be decommissioned in order to reduce cost and overall risk. Organizations that effectively undertake Application Realization direct resources to ensure both the reliability and uptime of business critical applications, and reduce infrastructure spend costs by strategic refactoring or decommission.
A company’s most important assets are its employees. The importance and value of
institutional knowledge — the comprehension of company processes, purposes, and
history — is often lost in employee turnover. Developing simple integrated methods for
collecting human input is a critical component in translating an organization’s interpersonal exchanges of knowledge into a tangible history of the organization. This information must be correlated with the technical attributes of applications in order to provide meaningful intelligence. This correlation can be an incredibly complex task for purely technical solutions to perform, as these solutions lack comprehension of the unique qualities of the business (i.e., the business’ organizational structure and its employees). What is required is a business-driven process, one to which
application discovery technology does not easily align or is capable to resolve.
Application Complexity
The enterprise state of network complexity requires solutions to find order within applications, but the reliance on technical solutions to discover applications is limited by the ability to incorporate both the political and social aspects of the business into the application equation: business + technology = application. Current solutions are often restricted in the data that they can acquire, catalog, and correlate, which limits their ability to see the application for what it is, whether that be a critical asset to the business, a serious security concern, or something in between.
Without some sort of integrated guidance on populating application profiles beyond technical attributes, a profile inaccurate to the business is constructed and is subsequently relied upon. The identity of interconnections, connections to other applications, the importance of those applications, and the likelihood of those connections being compromised are important data points that should be easily understood. Scenarios in which all application connections are identified solely based on network access provide an overly connected application profile, and not one that reflects expected and necessary operation of that application. This process is further complicated by aberrant behaviors, such as malware and misconfigurations, that mischaracterize an application’s connectivity, resulting in excessive and incorrect application connectivity needs. This inaccurate and non-contextualized view of an application is dangerous to the business, as decisions are subsequently made based on flawed data.
When an application is identified, the following questions should be asked and answered:
1. How is this application identified?
2. How is the purpose of the application understood?
3. What is the business value of this application?
4. Who is responsible for this application?
5. What security concerns are associated
with this application?
6. What is the broader impact of those security
concerns to other business applications?
7. Does this application require greater resiliency?
8. Should this application be refactored or removed?
The (Big) Data Problem
The network consists of an overwhelming amount of data, and is very rarely consistently managed and centralized. A wide variety of tools track network assets, sometimes centralized in traditional CMDBs. Different cloud consoles maintain inventory of cloud infrastructure. Ticketing systems create and maintain historical records of change requests. New applications are created relying on existing databases, and/or creating new ones. Business intelligence analysts establish their own servers and databases for reporting. Everything is everywhere, and the purpose of applications and application components are lost inside the heads of employees. While organizations develop new and more efficient ways to reduce network sprawl, they silo data across the network and, unintentionally, in its people. Data has not only increased in volume, but it has become more diverse in its location and purpose.
Change Management, Change Amnesia
Business inevitably undergoes change, and change to the business will continue to occur. Infrastructure is upgraded to ensure resiliency and patched as bugs are discovered and vulnerabilities are disclosed. Infrastructure migrates to new networks as the business changes and adopts the cloud. Old infrastructure is decommissioned (or thought to be decommissioned) in response to these changes. These continuously occurring changes are often disparately tracked and/or documented, communicated through email, or shared in meetings or conversations. The result is a standstill in decision making without the historical context to identify the broader impact and its severity when planning an upcoming change. When these changes do occur, applications may fail in seemingly mysterious ways, costing valuable labor to troubleshoot, or resulting in a loss of revenue.
The reliance on both historical layers of technology and multiple providers of the same technology for business continuity results in a hybrid network — hybrid in infrastructure types, hybrid in the technology that hosts and connects the infrastructure, and hybrid in management personnel. While the network scales to enable business operations, the network sprawls. The magnetic tape server farms have been replaced with mainframes, those mainframes have been deprecated in cloud adoption, and now Kubernetes infrastructure proliferates in the cloud. The network has sprawled both physically and virtually, has become more technically diverse, and has devolved into a less understood state as decisions have been made without the rationale of the implementation of those decisions being documented.
The layers of adopted technology, the creation of applications to take advantage of the adopted technology, the sprawl of application resource locations, and the turnover of employees that created or maintained those applications results in complexity. Without resolving this growing complexity, confidence in decision making and understanding the impact of changes erodes and prevents organizations from maintaining an agile state.
The Importance of Connectivity
Connectivity is often defined as “visibility” by vendors, but visibility is limited to rudimentary asset inventory and network protocols. Understanding application connectivity based solely on server connections is a challenge, as this “visibility” is inhibited by gaps in data and context that is not sufficiently understood. The output from this approach is an image of an application that no one fully understands or can interpret the risk of each individual connection.
The interconnectivity of applications and the organization further exacerbates this already impassible challenge, as an application or service may depend on another application or service, which may also depend on another application or
service creating a cascading effect of outages of varying and entirely unknown severity. The result of this uncertainty is assured complacency to avoid approving or making changes that cause the cascading effect that disrupts application connectivity or revenue production, increases the attack surface, and erodes resiliency.
When we enrich this connectivity to include ownership, business function, historical context and other data that may have been traditionally siloed the significance of application connections are truly understood. While the sprawl of the network still exists, the business and application-critical connections within it are well understood. Changes in network connections are undertaken without unintended indirect application dependency disruption. Communication during outages or other events is efficient, with clear understanding of ownership and business impact to each stakeholder.
Each connection must serve a purpose to the application, and that application must serve a purpose to the business. To understand these connections beyond the ports and protocols, within the perspective of the business is an absolute necessity for complete Application Realization.
Application Realization, a New Approach.
A new approach is required to solve the challenge of cataloguing applications to make informed and effective decisions about the application portfolio. A solution must resolve the technical complexity of the network, converge it with the consolidated sprawl of an organization’s assets, and enrich it with human-maintained knowledge. Application Realization provides the convergence of data, comprehension of connectivity, and the clarity of business outcomes.
The aggregator of technical and human-sourced information provides the single source of truth for the business. Centralized application information ensures consistent access to accurate data, data-driven decisions, and defensible positions. Beyond aggregation, Application Realization includes the study of how this data is interconnected to itself, the business and the people that maintain and utilize applications.
The ability to aggregate data, contextually correlate, and connect it to the business provides a comprehensive repository of applications. For broad organizational acceptance this repository must be easily accessible, convey actionable insights, and interpret relevant data for stakeholders. Such as to
establish the value of the application to the business, identify weaknesses of an application, or determine if the application can be decommissioned, whether for assurance or exploration.
Exploration is the critical component of Application Realization, and is a general necessity across all technology. For instance, Google Maps is trusted to be accurate in route planning because it updates as roads change, closures are added, and traffic patterns shift. This accuracy relies on the exploration of users to validate existing routes, identify new routes, and reflect the current capability of access based on traffic patterns. Why wouldn’t the same requirement be expected of applications deployed in constantly
changing networks?
Current solutions lack this important feature because they are unable to ingest the necessary application data, and cannot establish connections beyond technical attributes. Application discovery solutions require complicated query mechanisms, provide opaque reporting, and have onerous installs that create barriers for stakeholders to explore their data. Exploration must be simple for all stakeholders in any application, so that they can find and clarify information for other stakeholders. Exploration facilitates the capture of human knowledge that is often lost, and encourages future updates because of the ease of access and usability.
Applications should be identifiable through simple searches and not through complex structured queries. The manager of an applications team must identify what they are looking for as easily as their more technically immersed infrastructure engineer. Most important, the results must be in format and level of detail necessary for effective understanding.
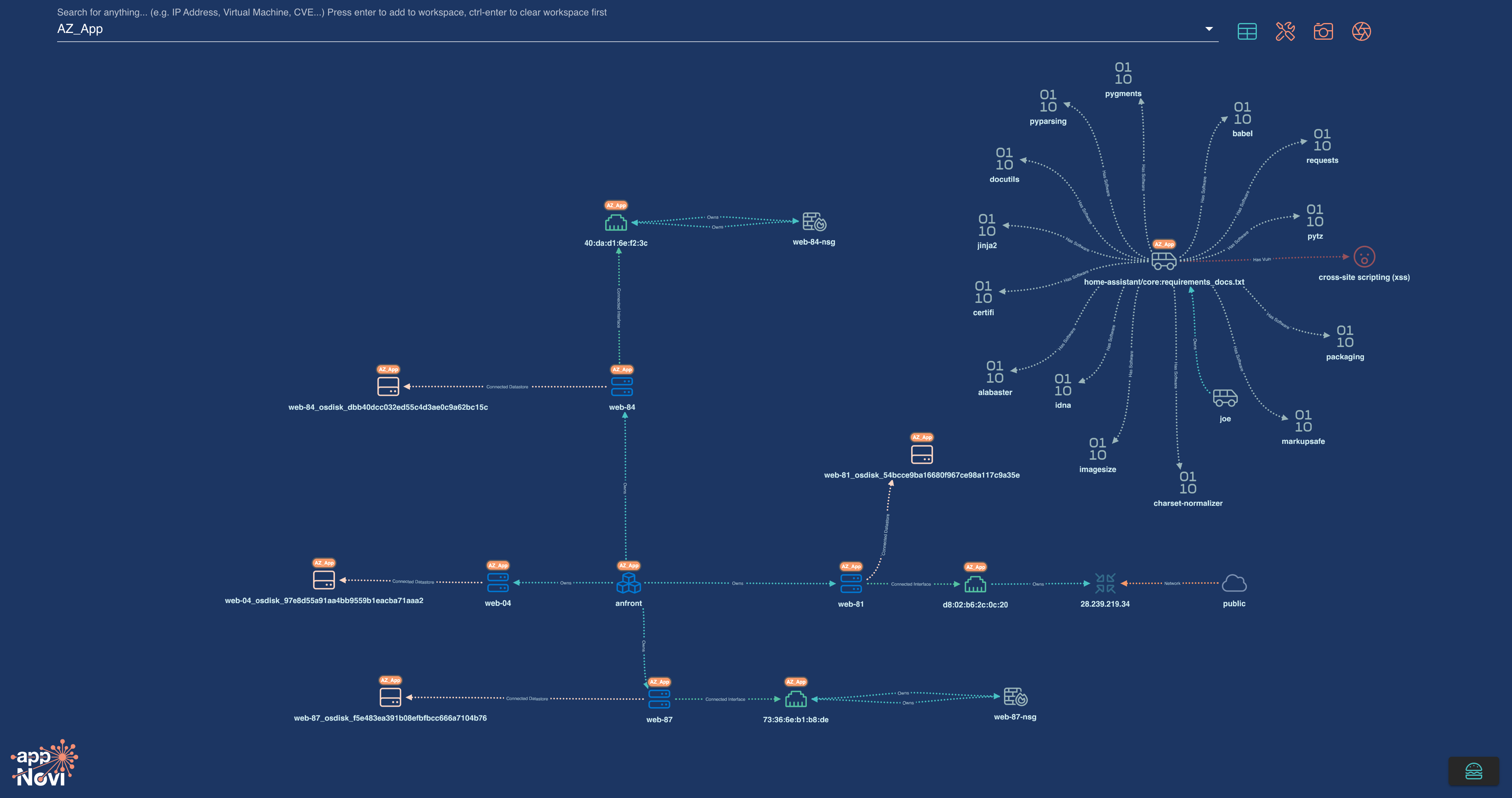
Visual representation of applications is critical. Humans are visual learners — we devote more brain usageto sight than any other sense, we process images faster than text, and we retain visual information with higher recall than information presented in any other medium. Yet current solutions are limited to tabular results, present unintuitive visualizations mired by complexity, and lack the ability to highlight relevant information to the proper stakeholders. Articulate visualization makes applications easy to understand, encourages exploration, and creates unique interactive artifacts that convey true stakeholder perspective.
Application Realization in Practice
CONSIDER A COMMON SCENARIO:
The vulnerability management team identifies a server in AWS to be vulnerable and requires a resolution to meet their SLA. The application owner is alerted and must provide a response within two days of whether an appropriate patch can be applied, or if other mitigating controls need to be put in place. However, the application owner inherited this application and is unfamiliar with the application’s purpose. The task at hand is to understand the impact, if any, of resolving the vulnerability by applying the appropriate patch. However, the business impact is uncertain — the purpose of this application is unknown, and the impact of upgrading the server may result in other inoperable applications that may also have a dependency on the vulnerable server. Organizations unable to undertake the exploratory process from this point fall into a category of “fortunate” for applying the patch with no reported outages, “vulnerable” for not patching the server because of the uncertainty of the outcome of changes, or at “financial loss” because the patch disrupts the application or others that shared the server as a dependency.
Application Realization
eliminates the reliance on good
fortune, and offers assurance
that, despite changes to
the business, the realized
applications empower the
business to make accurate and
effective decisions. Consider
the scenario above with
more context when it comes
to making a decision on the
upgrade of a server OS:
- Is the vulnerable server needed by the application?
- Does the vulnerable server support more applications than the one for which the application owner has been contacted?
- What is the importance and value of each of these applications to the business?
- Which parts of the business will be impacted if a change were to be applied?
- Rather than remediation, are there other options that would enable the effective mitigation of the vulnerability?
- Are the impacted applications important enough that the application and its components should be promoted for refactoring to increase the resiliency and security of the application, rather than merely applying patches every two weeks?
Although all questions may not be answered with the data immediately on hand, Application Realization consolidates the disparate business data and infrastructure data to provide a consolidated view where exploration is undertaken to answer these types of questions. Application Realization results in the effective disposition of issues raised by different stakeholders, and ensures the optimal allocation of resources to increase resiliency of the business’ applications while reducing expenditures on cloud infrastructure.
The Benefits of Application Realization
Application Realization resolves the lack of visibility and delivers business context for the organization beyond the point of implementation. Cataloguing applications and applying business-specific context results in operational efficiency that enables the business to scale without increasing risk or costs. While this aggregate data enables informed decision making, it prompts necessary action.
Providing accurate, contextual, and timely information enables businesses to react to change with greater efficiency and reduce risk. Whether it be a change to the network, a disclosure of a vulnerability, or a new business need, Application Realization provides consistent visibility through the unexpected. Achieved confidence and efficacy enable the business, reduce operational costs, and ensure business resiliency.
The most attractive aspect of undertaking Application Realization is that it is a simple implementation and configuration. Companies create and maintain data, and the flexibility for import and contextualization of this data with network data ensures effective data consolidation without high labor costs or redundancies in capabilities.
Application Realization is the simple solution for the enterprise’s complex application problems, and does not require new data or new customizations. Use the data you have today, and empower stakeholders across your organization to start Application Realization within 24 hours of installation.